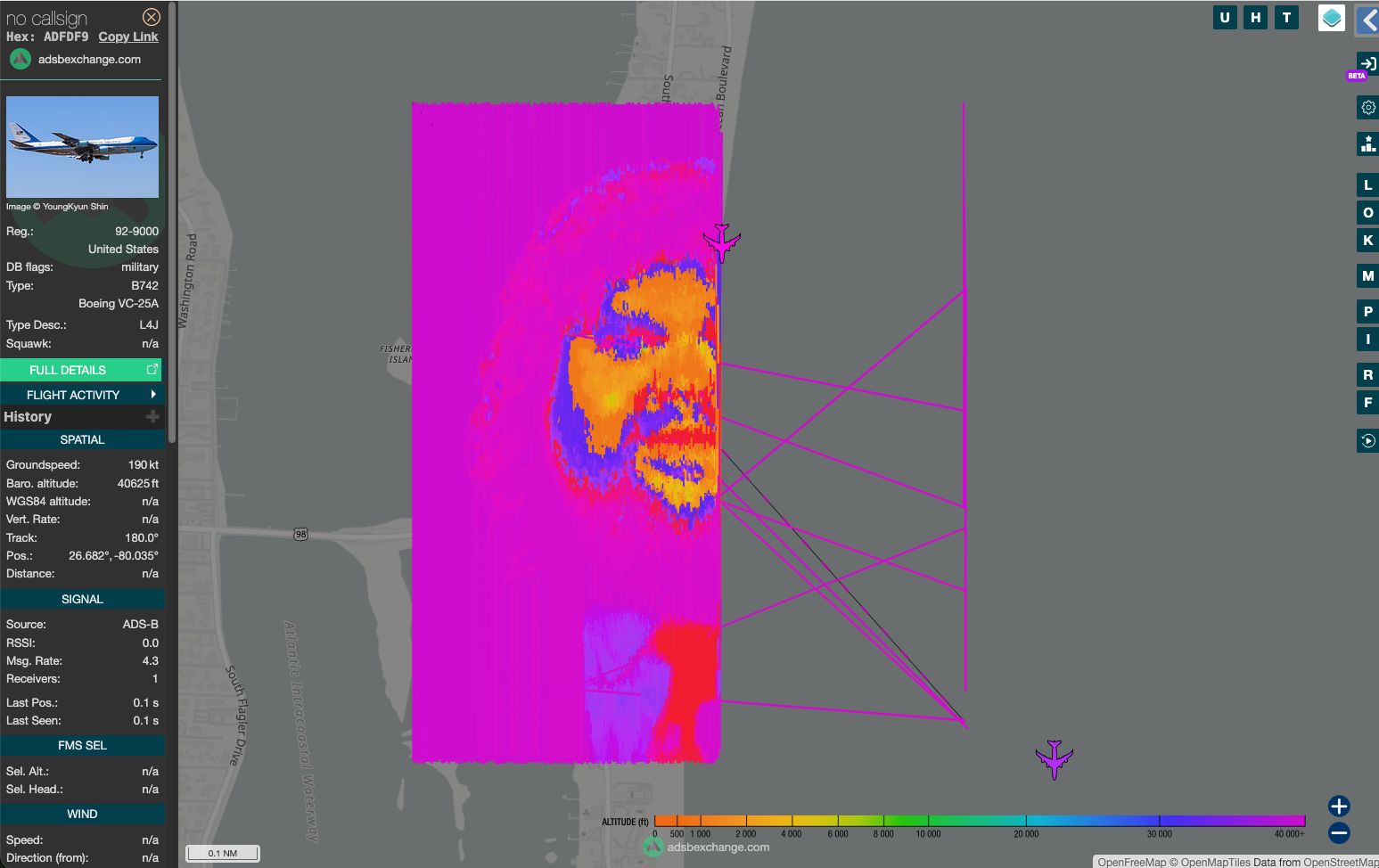
A digital ghost was the result of a sophisticated ADS-B spoofing attack on a flight tracking website.
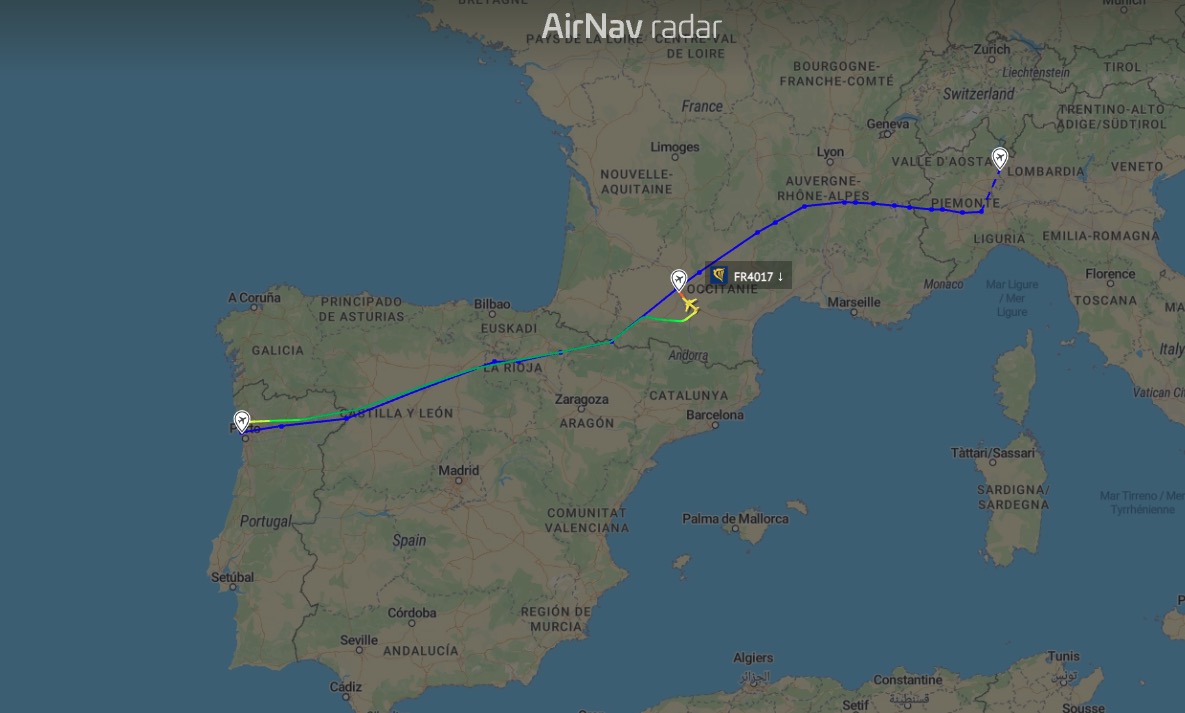
WASHINGTON D.C. — Aviation enthusiasts and flight trackers were met with a bizarre sight past week when a Boeing VC-25A—better known by its callsign AF1 or VANCE1—appeared to be performing highly coordinated, suggestive maneuvers over the United States.
The “VANCE1” Incident
The phantom aircraft appeared on ADS-B Exchange, a popular flight-tracking site used by hobbyists. By injecting false data into the network, the perpetrator was able to “draw” recognizable patterns on the live map by manipulating the reported coordinates and altitudes of the non-existent plane.
While the incident was a harmless, albeit crude, prank, it underscores a serious technical reality: the systems we use to track the world’s most important aircraft can be fooled.
How the Spoofing Works
To understand how this happened, we have to look at the two primary ways hackers and researchers manipulate location data: GPS Spoofing and RF ADS-B Spoofing.
1. ADS-B Spoofing (The Network Injection)
In this specific case, the “hack” likely didn’t happen in the sky, but on the ground. Automatic Dependent Surveillance-Broadcast (ADS-B) is the system aircraft use to broadcast their position to ground stations.
- Network Injection: Most tracking sites rely on a network of crowdsourced feeders (people with cheap SDR receivers). If a feeder injects falsified data directly into their software, the central network perceives it as a real signal.
- Protocol Vulnerability: ADS-B signals are unencrypted and unauthenticated. There is no “digital signature” to prove a signal actually came from a Boeing 747 rather than a laptop in a basement.
2. GPS Spoofing (The Physical Attack)
While the “VANCE1” prank was likely a data injection, GPS spoofing is a more aggressive physical-layer attack. This involves broadcasting a fake satellite signal that is stronger than the real one.
- The “Takeover”: A spoofing device mimics the timing and frequency of GPS satellites. The aircraft’s receiver locks onto the fake signal, believing it is in a different location.
- The Danger: Unlike network injection—which only fools people watching a website—GPS spoofing can fool the actual pilots and navigation systems on a real plane, potentially leading them off course.
Comparison: Spoofing vs. Jamming
| Feature | Jamming | Spoofing |
| Method | Drowning out signals with “noise.” | Sending fake, “believable” data. |
| Goal | To deny service (make GPS fail). | To deceive (make GPS give wrong info). |
| Detection | Easy; the system simply stops working. | Difficult; the system thinks it’s working fine. |
The Aftermath
ADS-B Exchange and similar platforms have historically resisted filtering data, preferring to show exactly what the receivers pick up—”the good, the bad, and the fake.” With Wingbits’ secure, high-precision devices, attempts to feed false positions into the network become far more difficult.
While the Air Force has not officially commented on the “VANCE1” ghost track, the event serves as a reminder that as our skies become more digital, the potential for electronic “graffiti” grows. For now, the only thing that actually took a hit was the dignity of the world’s most famous callsign.